On April 18–19, an attacker drained 116,500 rsETH from Kelp DAO’s LayerZero-based bridge, roughly 18% of the token’s supply and about $292–293 million at the time. The bridge held reserves backing rsETH on more than 20 networks, so the exploit instantly created doubts about whether wrapped rsETH on those chains still had real backing behind it.
Singapore Summit: Meet the largest APAC brokers you know (and those you still don't!)
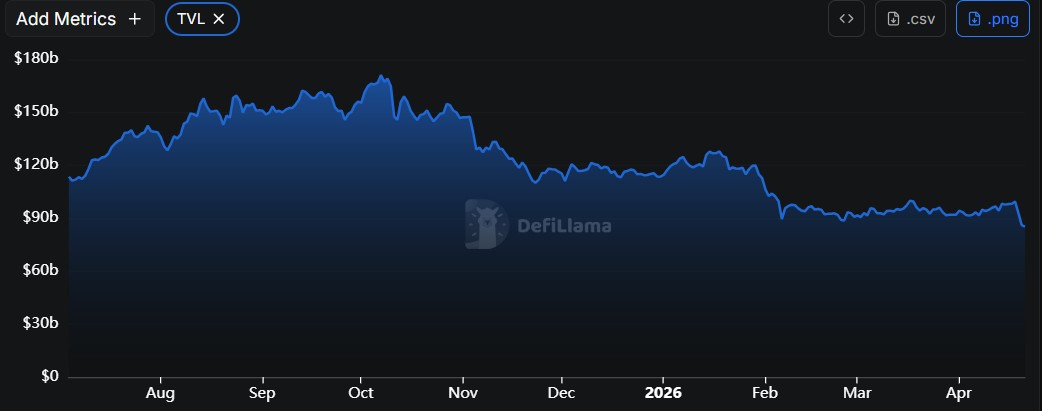
According to DeFiLlama data, the Kelp DAO exploit landed in a market that was already near the psychological $100 billion milestone for total value locked, and it erased almost $14 billion from that figure within a day. Between April 18 and 19, DeFi’s aggregate TVL fell from about $99.5 billion to roughly $85.21 billion.
- Why DEXs Are Trying to Reproduce FX Market Behaviour
- What WeFi Means for Anyone Chasing Better Exchange Rates
- Falcon Finance Establishes Onchain Insurance Fund with Initial $10m Contribution
Hack Shakes DeFi, Wipes $14B TVL
The technical root cause looks simple on paper: Kelp ran a 1‑of‑1 verifier configuration for LayerZero’s Decentralized Verifier Network. Only one verifier needed to sign off on cross‑chain messages, so once the attacker controlled that view of the world, they effectively controlled the bridge.
According to several post‑mortems, the attacker compromised two RPC nodes that fed data to the verifier and then used a DDoS attack to knock clean nodes offline, forcing a failover to their poisoned infrastructure. From there, they injected a forged cross‑chain message that tricked the system into releasing 116,500 rsETH to their address, all without breaking a single line of on‑chain code.
Read more: If DeFi Had This in 2022, Maybe It Wouldn’t Have Collapsed
From an analytical standpoint, this hack sits in the same family as earlier bridge failures such as Ronin and Nomad, where central checkpoints and initialization assumptions became high‑value targets. The common pattern is not a single vulnerable contract but an architecture that treats critical verification as a convenience feature rather than a hardened security boundary.
Lending Models Under Pressure
The story did not end at the bridge. The attacker rapidly moved the stolen rsETH into Aave as collateral and borrowed large amounts of ETH against it, while opening positions on other lending markets.
Investors reacted quickly. On‑chain data and market reports show that more than $5.4 billion exited Aave in short order as users reduced risk, with total value locked dropping even more sharply over 48 hours.
ETH utilization on Aave briefly spiked to 100%, and AAVE’s token price fell around 10% as traders priced in both the immediate hole and future governance decisions around recapitalization. From a market‑structure perspective, this looks less like a one‑off exploit and more like a stress test of the non‑isolated lending model where one asset’s failure can ripple across an entire pool.
He pointed to Aave v4’s planned “hub‑and‑spoke” architecture—closer to semi‑isolated markets—as a potential compromise between composability and safety. The underlying analytical point is that lending protocols may no longer afford to assume that all whitelisted collateral assets share roughly the same risk profile, especially when some sit on complex, cross‑chain restaking rails.
A Security Reckoning in an AI Age
The Kelp DAO exploit lands in a month where crypto platforms have already lost hundreds of millions of dollars to hacks, piling onto a multi‑year trend of bridge‑centric incidents.
Whether or not AI played a direct role in this particular hack, the pattern of rapid, multi‑venue attacks suggests defenders can no longer rely on slow human review and ad‑hoc configuration choices to keep up. For DeFi builders, the practical takeaway is less about any single tool and more about assuming that motivated attackers can see the system almost as clearly as its designers.
The public blame game between Kelp DAO and LayerZero underscores another uncomfortable reality: responsibility for security in composable finance is shared, but accountability often fragments once something breaks.
Kelp says it followed LayerZero’s defaults and common practice; LayerZero says it warned against single‑verifier setups and now promises to stop signing messages for such configurations. For users and institutional participants, this dispute matters less than the broader lesson: default settings on critical infrastructure are de facto risk decisions, not neutral technical details.


















