Lukas Stefanko, a renowned malware researcher, published a report earlier this week revealing that he had discovered not one, not two, not three, but four fake cryptocurrency wallets on the Google Play Store.
Fake #cryptocurrency wallets found on Google Play Store.
These app were created using Drag and Drop service - anyone can be malware "developer" and upload it to Play Store now.https://t.co/ELyHDt9DZw — Lukas Stefanko (@LukasStefanko) November 13, 2018
“These threats imitate legitimate services for NEO, Tether and MetaMask. I reported these apps to Google security team and they were promptly removed,” he wrote on his personal website, adding that they were promptly removed from the store.
Stefanko added that the thing that concerned him the most was that each one of these applications was created with a Drag-n-Drop app builder service. In other words, no coding skills were required to create the malware - practically anyone could create similar scams.
Fake Apps Attempted Phishing , Theft
Stefanko sorted the fake apps into two separate categories: phishing and fake wallets. The app imitating MetaMask was classified as a “phishing” app. After launching, the app “requests from the user his Private Key and wallet password.”
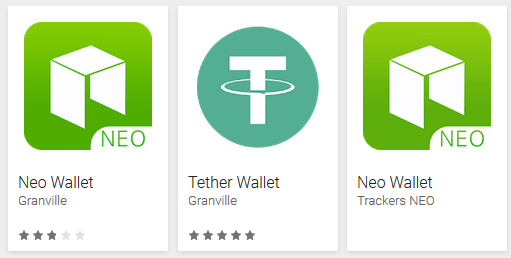
A screenshot of the fake wallets, as posted on Stefanko's personal website.
The fake wallet apps fool users by listing the attacker’s public address as the public address of their newly-generated wallet. Users are not given access to their private keys.
“If a user send [sic] his funds to this wallet, he is not able to withdraw them because, [sic] he doesn’t own private key,” Stefanko explained. He published screenshots of two separate accounts that he created on the app, both of which were assigned the same public address.
Distributing Malware Has Become Increasingly Easy
Stefanko’s comments about the ease with which these fake apps were created echoed the sentiments of Rick McElroy, strategist at cybersecurity firm Carbon Black.
McElroy commented to CNBC earlier this year that distributing malware was extremely easy--although the methods that he identified were a bit different. McElroy and his firm published a report showing the ease with which any person could purchase a piece of malware from the “deep web” and begin operating it, adding that some of the malware even comes with technical support.